TrueCommand Nightly Development Documentation
This content follows experimental early release software. Use the Product and Version selectors above to view content specific to a stable software release.
LDAP Servers
3 minute read.
Last Modified 2024-03-28 08:39 EDTUsers can configure TrueCommand to use LDAP servers for security and authentication management among connected TrueNAS systems.
Click the gear icon in the upper toolbar and select Administration. Scroll down to the LDAP Servers widget and click ADD.
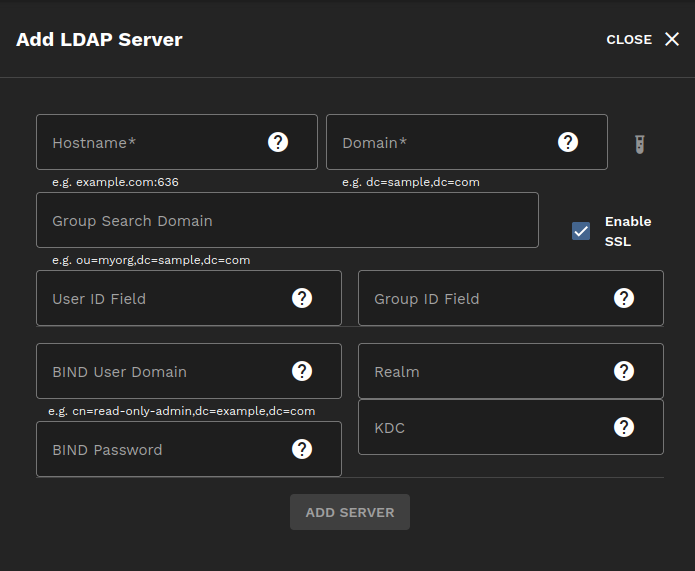
| Setting | Description |
|---|---|
| Hostname | Host name of LDAP/AD server, with optional port. e.g. example.com:636. |
| Domain | LDAP base domain. e.g. dc=example,dc=com. |
| Group Search Domain | Optional for admins who want to avoid issues with unwanted groups by forcing group searches to start at a deeper domain. |
| User ID Field | Class mapped to login username. The default is uid. |
| Group ID Field | Class for finding groups associated with a user. The default is cn. |
| BIND User Domain | Full user domain for binding before finding user fully qualified ID (FQID). Optional. |
| BIND Password | If the bind user is set, use this password when performing a simple bind on user search. |
| Realm | The realm that performs authentication against the LDAP server. |
| KDC | The Kerberos Key Distribution Center that supplies session tickets and temporary session keys to users and computers within the LDAP server. |
| Enable SSL | Enable LDAPS/TLS connection. Uses the globally configured verification settings. |
After you fill the form according to your server, click ADD SERVER.
Click CONFIGURE in the Configuration widget and enable Allow LDAP user creation, then click SAVE.
TrueCommand only checks for usernames, passwords, and groups while authenticating LDAP credentials. You may add entries for email, phone number, or URLs, but TrueCommand does not check for them.
The LDAP server uses an LDAP Data Interchange Format (LDIF) file to add or modify entries in the server.
For more in-depth LDAP configuration methods, see this LDAP System Administration guide.
Enter the following command to add entries to the LDIF file. Separate specifications (cn, dc, etc.) with a comma.
$ ldapmodify -D "uid=USER,dc=DOMAIN,dc=DOMAIN" -w secret \
> -x -a -f /tmp/users.ldif
USER is the user ID.
DOMAIN is a domain component like com, edu, org, etc.
If the command succeeds, you see an output like this:
adding new entry "uid=USER,dc=DOMAIN,dc=DOMAIN"
If, for instance, the user you added does not yet have a password, you can add it with the following command.
dn: uid=USER,dc=DOMAIN,dc=DOMAIN"
changetype: modify
add: password
password: USER@DOMAIN.DOMAIN
For finding associated groups, TrueCommand looks for groupOfUniqueNames, groupOfNames, posixGroup, and Group object classes and users matching the uniquemember, member, owner, or memberUid attributes.
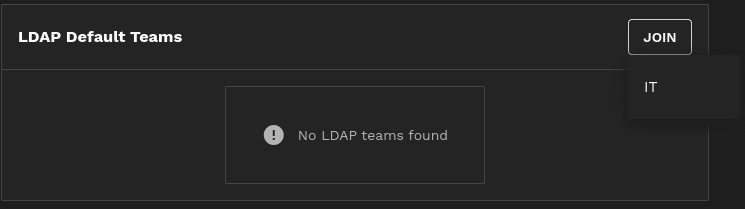
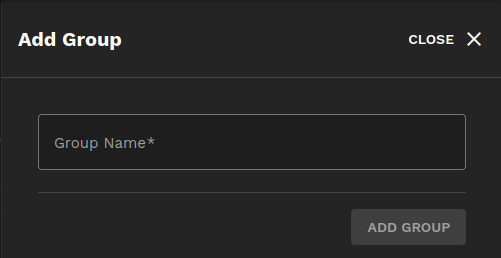
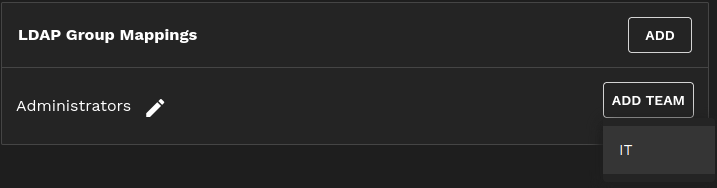
Teams configured under LDAP Default Teams are added to new users automatically, while group names can be mapped to one or more teams under LDAP Group Mappings.
The two most prominent error codes for LDAP are 254 (connection failure), and 49 (invalid credentials).
In the event of a connection failure, ensure Enable SSL is checked if only LDAPS is available.
For credential failures, ensure you have set the right authentication mode, either BIND password or Kerberos.
If Kerberos is enabled, we recommend using it.
If password servers are required, move the autogenerated krb5.conf within the container from /etc/krb5.conf to /data and enable it by setting --env KRB5_CONFIG=/data/krb5.conf on a new container run. See the Middleware log for further debugging.
Some AD servers require manually setting the SASL environmental variable to --env LDAPSASL_SECPROPS=minssf=0,maxssf=0 to disable security factor limitations and avoid an “illegal packet length” error.
You can configure other ldap.conf settings this way, or set the LDAPCONF environment variable to /data/ldap.conf and write a custom conf there.
TrueCommand sets TLS_REQCERT and TLS_REQSAN to ‘allow’ or ‘demand’ depending on global TLS settings. It also sets TLS_CERT and TLS_KEY to the MW-managed self-signed certificate in /data/truecommand.

