TrueNAS SCALE Nightly Development Documentation
This content follows experimental early release software. Use the Product and Version selectors above to view content specific to a stable software release.
Idmap Screens
8 minute read.
Last Modified 2024-07-24 15:53 EDTIdmap in Linux is essentially a translation of a range of IDs into another or the same range of IDs.
Only administrators experienced with configuring Id mapping should attempt to add new or edit existing idmaps. Misconfiguration can impact system operation.
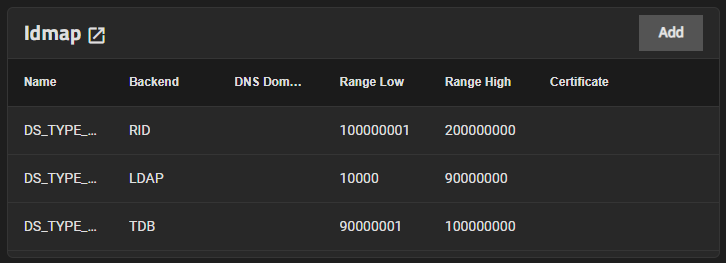
The Idmap widget in the Advanced Settings on the Directory Services screen displays idmaps added to SCALE.
Add opens the Add Idmap configuration screen.
Click on any instance to open the Edit Idmap screen.
The Idmap widget header opens the Idmap screen.
The Idmap screen displays a list view of idmaps configured on your SCALE system.
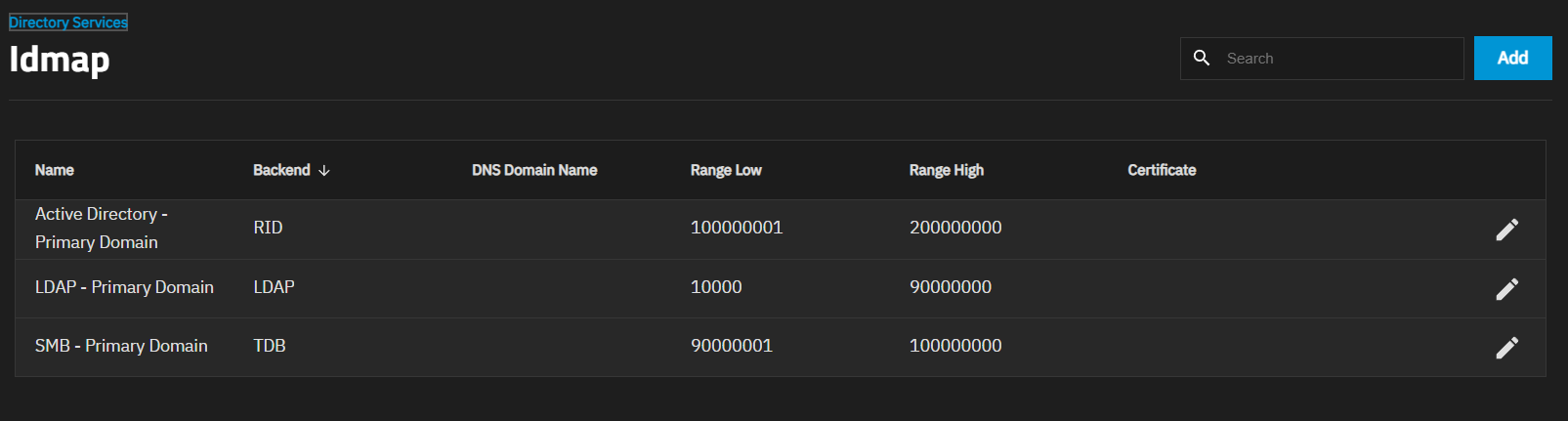
Add opens the Add Idmap screen.
Click on an Idmap on the widget to open the screen for the selected idmap.
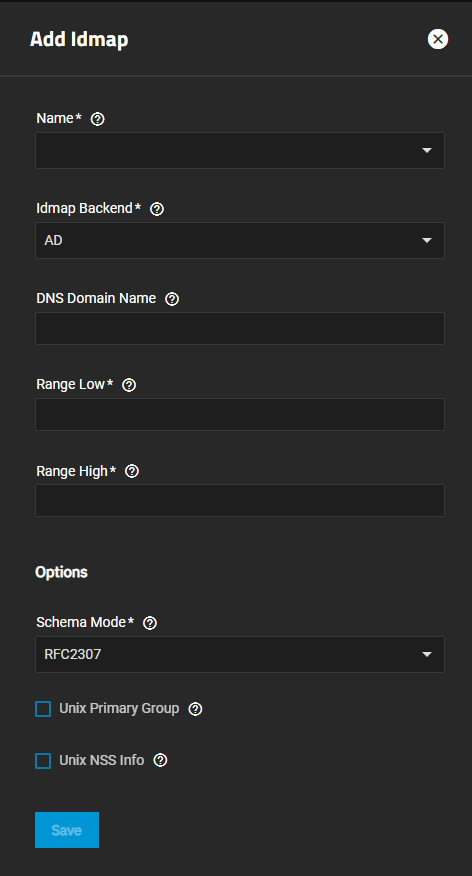
The settings on the Add Idmap and Edit Idmap change based on the selection made in both the Name and Idmap Backend fields.
| Setting | Description |
|---|---|
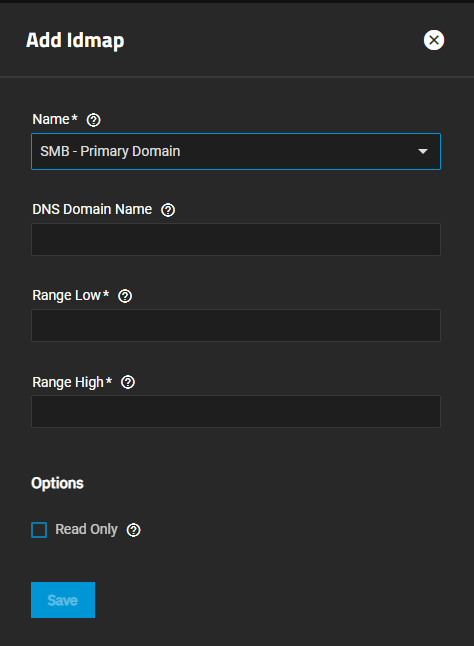
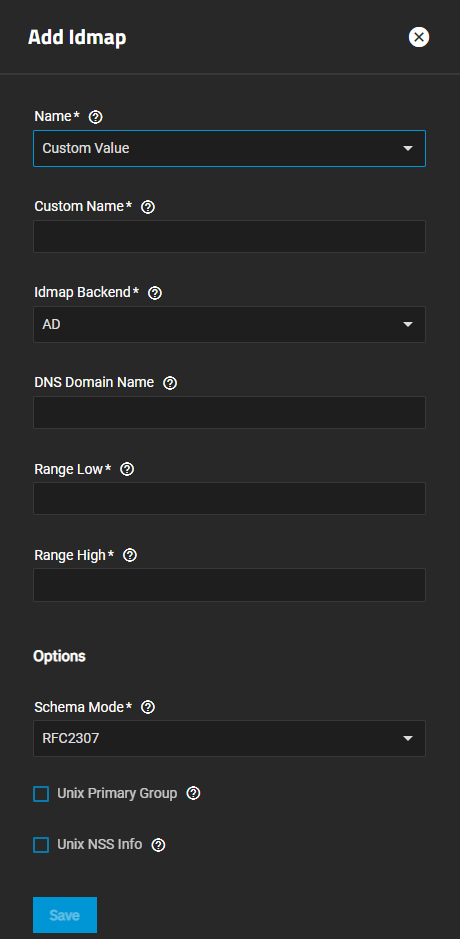
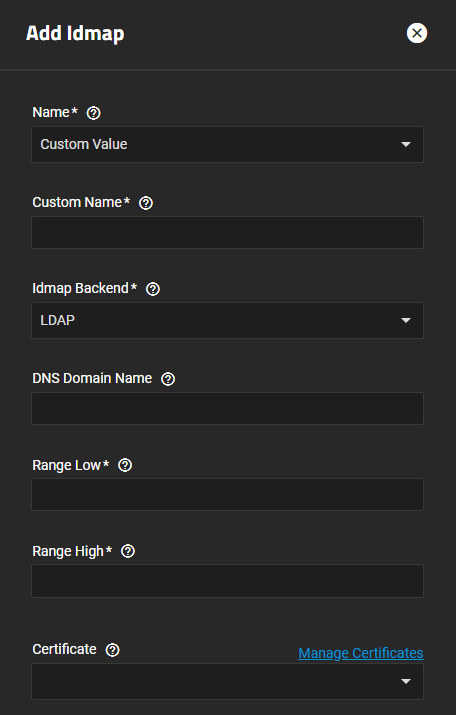
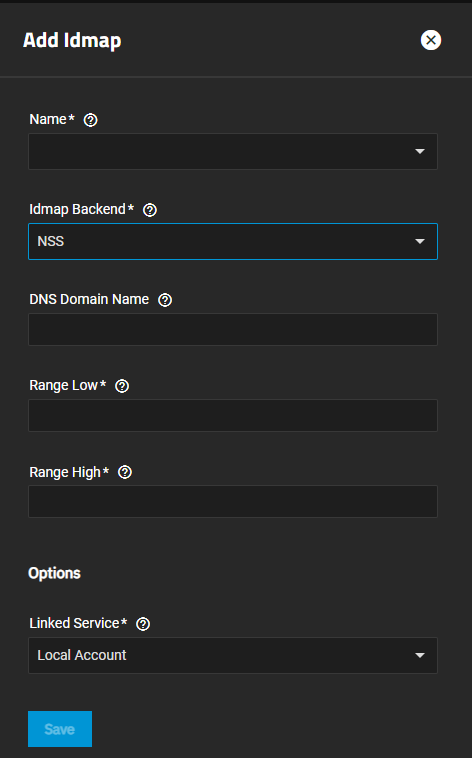
| Name | (Required) Select an option from the dropdown list, SMB - Primary Domain or Custom Value. SMB - Primary Domain reduces the fields displayed on the Add Idmap screen. Selecting Custom Value adds The Custom Name field. |
| Custom Name | Displays below the Name field after selecting Custom Value in the Name field. Enter the pre-Windows 2000 domain name. |
| Idmap Backend | (Required) Select the backend plugin interface for Winbind to use to store SID to UID/GID mapping tables. The correct setting depends on the environment you deployed the NAS in. Options are AD for Active Directory, LDAP for an LDAP environment. AUTORID is similar to RID but it can automatically assign IDs for different domains. NSS provides a means to map Unix users and groups to Windows accounts. RFC2307 provides a way for Winbind to read ID mappings from records in an LDAP server defined in RFC 2307. RID provides a way to use an algorithmic mapping scheme to map UIDs/GIDs and SIDs. TDB is similar to RID but it is an allocating backend, which means it needs to allocate new users and group IDs in order to create new mappings. The selected option changes the settings displayed on the Add Idmap screen. |
| DNS Domain Name | Enter the DNS name of the domain. |
| Range Low | (Required) Enter a value for the least number of members. Works with the Range High to establish the range of UID/GID numbers the Idmap backend translates. If an external credential like a Windows SID maps to a UID or GID number outside this range, TrueNAS ignores it. |
| Range High | (Required) Enter a value for the greatest number of members. Works with the Range Low to establish the range of UID/GID numbers the Idmap backend translates. If an external credential like a Windows SID maps to a UID or GID number outside this range, TrueNAS ignores it. |
Options Settings The Options settings change based on the selected Name and Idmap Backend fields.
| Setting | Description |
|---|---|
| Unix Primary Group | Select to fetch the primary group membership from the LDAP attributes (gidNumber). If unselected, the primary group membership is calculated via the primaryGroupID LDAP attribute. |
| Unix NSS Info | Select sets Winbind to retrieve the login shell and home directory from the LDAP attributes. If unselected, when the AD LDAP entry lacks the SFU attributes the smb4.conf parameters template shell and template homedir are used. |
Support for LDAP Schema Mode for SMB shares is deprecated in TrueNAS SCALE 22.02 (Angelfish) and removed in 24.10 (Electric Eel). Before updating to 24.10 or later, Administrators using this legacy feature should stop using SMB shares (continue using LDAP), convert directory users to local TrueNAS accounts (stop using LDAP), or convert to Active Directory (stop using LDAP).
The settings for Add Idmap displays a subset of those on the default screen.
The Add Idmap screen with Name set to Custom Value and Idmap Backend set to AD shares the same settings as the default screen but it includes DNS Domain Name.
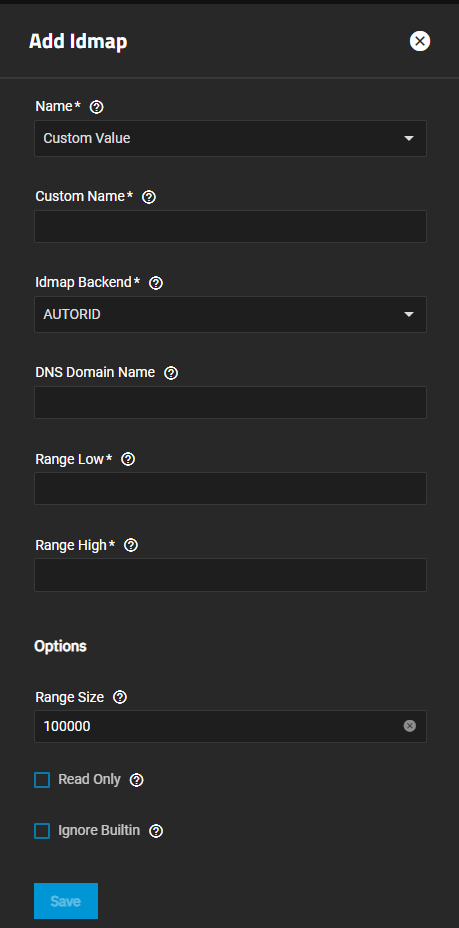
The Add Idmap screen with Name set to Custom Value and Idmap Backend set to AUTORD shares the some of the same settings on the AD screen but the Options settings are different.
The Add Idmap screen with Name set to Custom Value and Idmap Backend set to LDAP shares the some of the same settings on the AD screen but it adds the Certificate option, and the Options settings are different.
The Add Idmap screen with Name set to Custom Value and Idmap Backend set to NSS shares the same settings as the AD screen. There is only one Options setting.
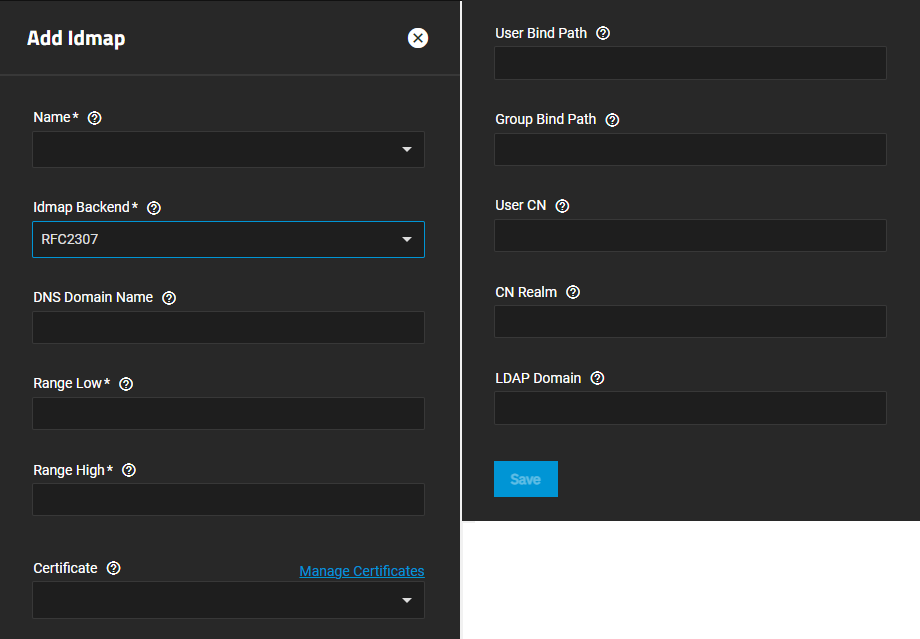
The Add Idmap screen with Name set to Custom Value and Idmap Backend set to RFC2307 shares the same settings as the LDAP screen, and some of the same Options settings.
The Add Idmap screen with Name set to Custom Value and Idmap Backend set to RID shares the same settings as the AD screen. There is only one Options setting.
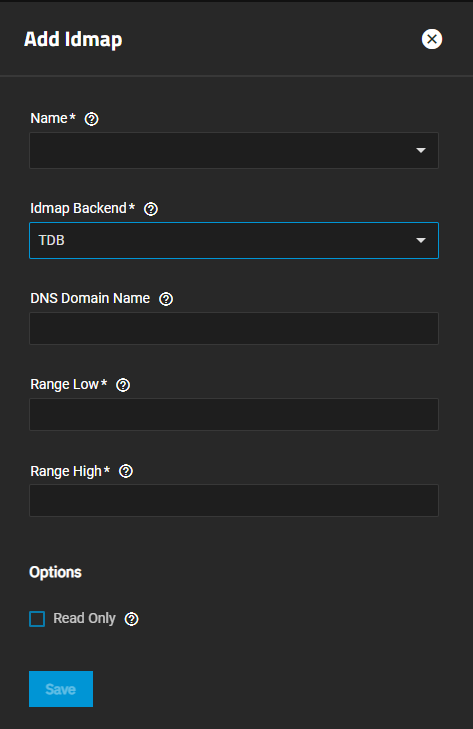
The Add Idmap screen with Name set to Custom Value and Idmap Backend set to TDB shares the same settings as the AD screen. There is only one Options setting.