TrueNAS CORE Nightly Development Documentation
This content follows experimental early release software. Use the Product and Version selectors above to view content specific to a stable software release.
Certificates
4 minute read.
Last Modified 2024-03-15 13:07 EDT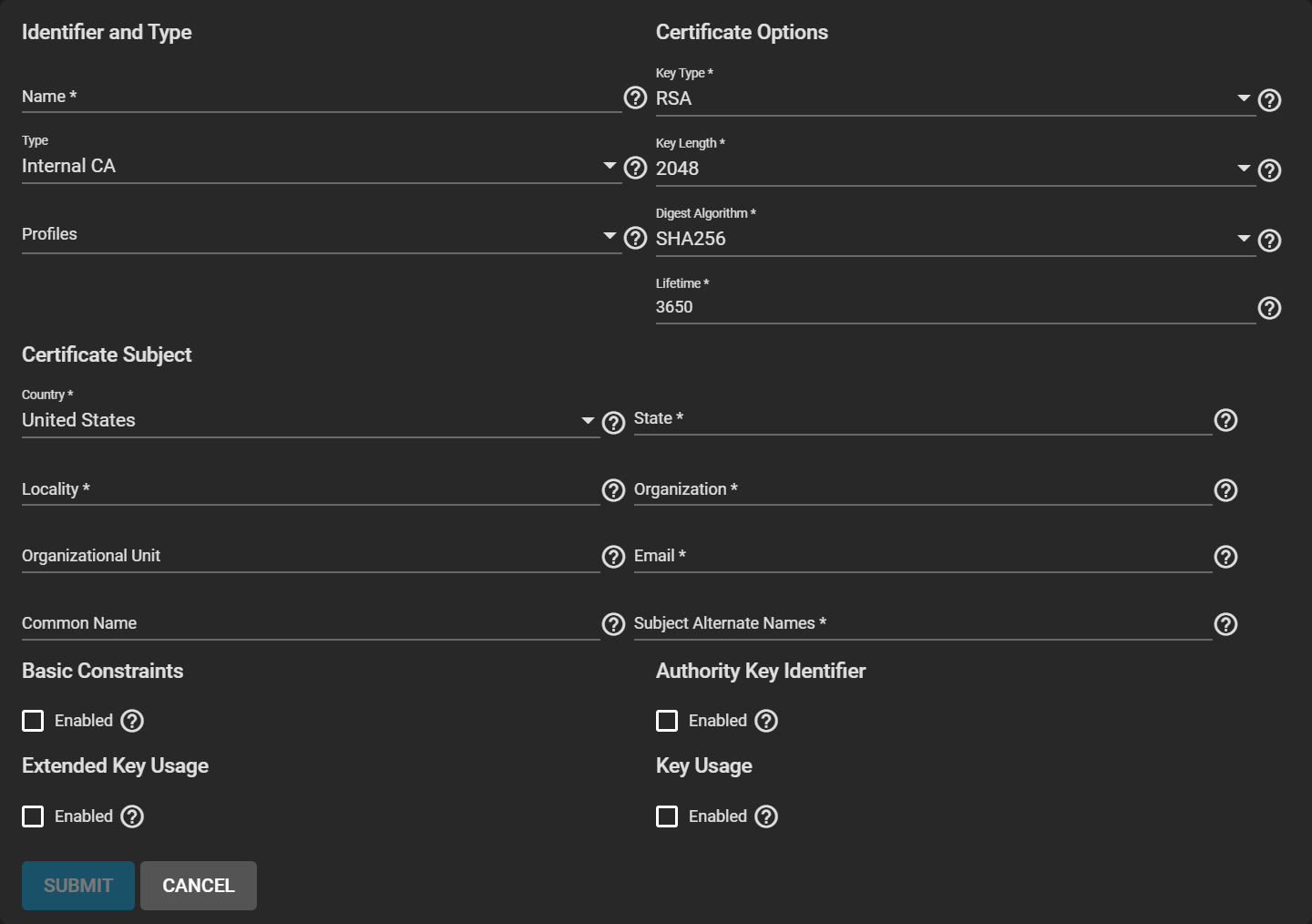
| Name | Description |
|---|---|
| Name | Descriptive identifier for this certificate. |
| Type | Internal Certificate is used for internal or local systems. Certificate Signing Request is used to get a CA signature. Import Certificate allows an existing certificate to be imported onto the system. Import Certificate Signing Request allows an existing CSR to be imported onto the system. |
| Profiles | Predefined certificate extensions. Choose a profile that best matches your certificate usage scenario. |
| Name | Description |
|---|---|
| Signing Certificate Authority (Internal Certificate) | Select a previously imported or created CA. |
| Key Type | See Why is elliptic curve cryptography not widely used, compared to RSA? for more information about key types. |
| EC Curve | Brainpool curves can be more secure, while secp curves can be faster. |
| Key Length | The number of bits in the key used by the cryptographic algorithm. For security reasons, a minimum key length of 2048 is recommended. |
| Digest Algorithm | The cryptographic algorithm to use. The default SHA256 only needs to be changed if the organization requires a different algorithm. |
| Lifetime | The lifetime of the CA specified in days. |
| Name | Description |
|---|---|
| Country | Select the country of the organization. |
| State | Enter the state or province of the organization. |
| Locality | Enter the location of the organization. For example, the city. |
| Organization | Enter the name of the company or organization. |
| Organizational Unit | Organizational unit of the entity. |
| Enter the email address of the person responsible for the CA. | |
| Common Name | Enter the fully-qualified hostname (FQDN) of the system. This name must be unique within a certificate chain. |
| Subject Alternate Names | Multi-domain support. Enter additional domains to secure. Separate domains by pressing Enter. For example, if the primary domain is example.com, entering www.example.com secures both addresses. |
| Name | Description |
|---|---|
| Enabled | Activate this certificate extension. |
| Path Length | How many non-self-issued intermediate certificates that can follow this certificate in a valid certification path. Entering 0 allows a single additional certificate to follow in the certificate path. Cannot be less than 0. |
| Basic Constraints Config | The basic constraints extension identifies whether the subject of the certificate is a CA and the maximum depth of valid certification paths that include this certificate. See RFC 3280, section 4.2.1.10 for more information. |
| Name | Description |
|---|---|
| Enabled | Activate this certificate extension. |
| Authority Key Config | The authority key identifier extension provides a means of identifying the public key corresponding to the private key used to sign a certificate. This extension is used where an issuer has multiple signing keys (either due to multiple concurrent key pairs or due to changeover). The identification MAY be based on either the key identifier (the subject key identifier in the issuer’s certificate) or on the issuer name and serial number. See RFC 3280, section 4.2.1.1 for more information. |
| Name | Description |
|---|---|
| Enabled | Activate this certificate extension. |
| Usages | Identify the purpose for this public key. Typically used for end entity certificates. Multiple usages can be selected. Do not mark this extension critical when the Usage is ANY_EXTENDED_KEY_USAGE. Using both Extended Key Usage and Key Usage extensions requires that the purpose of the certificate is consistent with both extensions. See RFC 3280, section 4.2.1.13 for more details. |
| Critical Extension | Identify this extension as critical for the certificate. Critical extensions must be recognized by the certificate-using system or this certificate will be rejected. Extensions identified as not critical can be ignored by the certificate-using system and the certificate still approved. |
| Name | Description |
|---|---|
| Enabled | Activate this certificate extension. |
| Key Usage Config | The key usage extension defines the purpose (e.g., encipherment, signature, certificate signing) of the key contained in the certificate. The usage restriction might be employed when a key that could be used for more than one operation is to be restricted. For example, when an RSA key should be used only to verify signatures on objects other than public key certificates and CRLs, the Digital Signature bits would be asserted. Likewise, when an RSA key should be used only for key management, the Key Encipherment bit would be asserted. See RFC 3280, section 4.2.1.3 for more information. |
| Name | Description |
|---|---|
| CSR exists on this system | Check this box if importing a certificate for which a CSR exists on this system |
| Signing Certificate Authority | Select a previously imported or created CA. |
| Name | Description |
|---|---|
| Certificate (Import Certificate) | Paste the certificate for the CA. |
| Signing Request (Import CSR) | Paste the contents of your Certificate Signing Request here. |
| Private Key | Paste the private key associated with the Certificate when available. Please provide a key at least 1024 bits long. |
| Passphrase | Enter the passphrase for the Private Key. |
| Confirm Passphrase | Confirm the passphrase for the Private Key. |

