TrueNAS CORE Nightly Development Documentation
This content follows experimental early release software. Use the Product and Version selectors above to view content specific to a stable software release.
Setting Up Users and Groups
4 minute read.
Last Modified 2024-03-21 13:55 EDTCreating users and assigning them to groups allows you to efficiently tune permissions and share data for large numbers of users.
Only the root user account can log in to the TrueNAS web interface.
When the network uses a directory service, import the existing account information using the instructions in Directory Services. Using Active Directory requires setting Windows user passwords inside Windows.
To see user accounts, go to Accounts > Users.
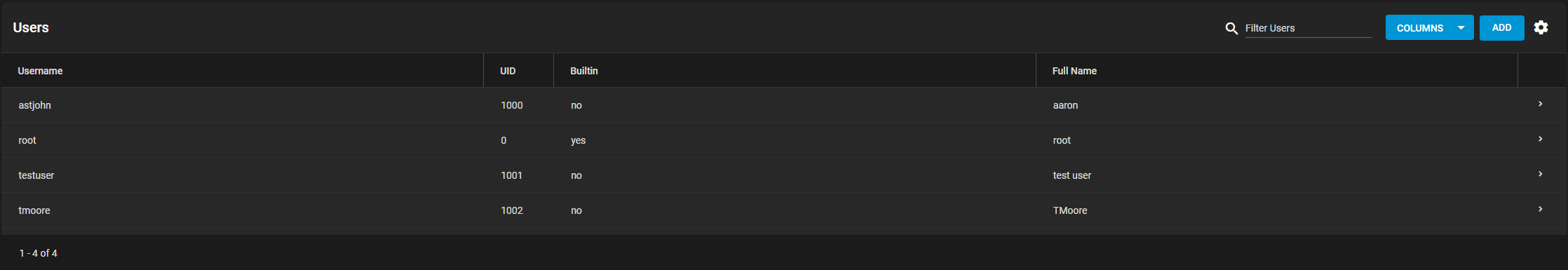
TrueNAS hides all built-in users by default. To see all built-in users, click settings and SHOW.
Go to Accounts > Users and click ADD.
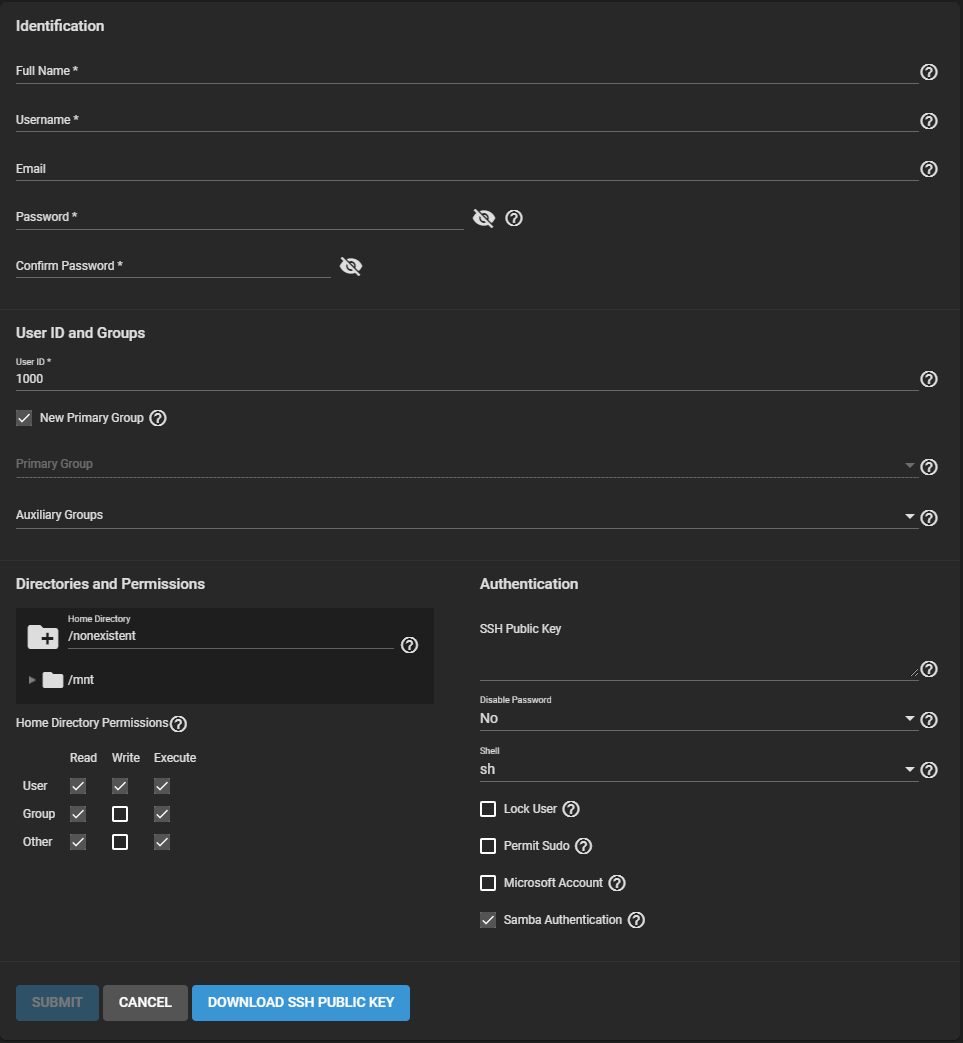
Fields with an * must be configured to submit or change the UI configuration.
TrueNAS subdivides account options into groups of similar options.
Enter a Full Name. TrueNAS suggests a simplified Username from the Full Name, but you override it with your own choice.
You can associate an Email address with a user account.
Set and confirm the user password.
Next, you must set a user ID. TrueNAS automatically suggests the user ID starting at 1000, but you can change it. We recommend using an ID of 1000 or more for non-built-in users.
By default, TrueNAS creates a new primary group with the same name as the user. To add the user to an existing primary group instead, unset New Primary Group and select a group from the Primary Group drop-down. You can add the user to more groups using the Auxiliary Groups drop-down.
When creating a user, TrueNAS sets the home directory path to
Directly under the file browser, you can set the home directory permissions. TrueNAS default user accounts cannot change their permissions.
You can assign a public SSH key to a user for key-based authentication by pasting the public key into the SSH Public Key field.
If you are using an SSH public key, always keep a backup.
Click DOWNLOAD SSH PUBLIC KEY to download the pasted key as a
When Disable Password is Yes, the Password field is unavailable. The system removes the existing password from the account and disables the Lock User and Permit Sudo options. The account can’t use password-based logins for services. For example, disabling the password prevents using account credentials to log in to an SMB share or open an SSH session on the system. By default, Disable Password is No.
You can set a specific shell for the user from the Shell dropdown:
Setting Lock User disables all password-based functionality for the account until you unset the option.
Permit Sudo allows the account to act as the system administrator using the sudo command.
For better security, leave this option disabled.
If the user account is accessing TrueNAS data using a Windows 8 or newer client, set Microsoft Account to enable additional authentication methods available from those operating systems.
By default, Samba Authentication is enabled. It allows users to access SMB share data using account credentials.
Using groups in TrueNAS is an efficient way to manage permissions for many similar user accounts. The interface lets you manage UNIX-style groups. If the network uses a directory service, import the existing account information using the instructions in Active Directory.
To see saved groups, go to Accounts > Groups
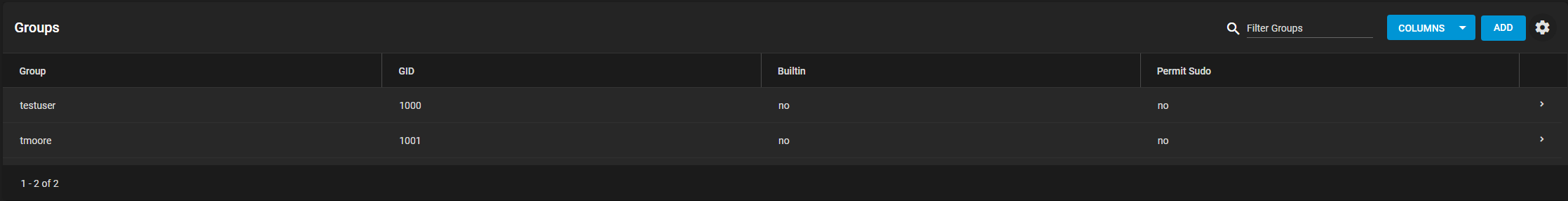
By default, TrueNAS hides built-in groups. To see built-in groups, click settings and SHOW.
Go to Accounts > Groups and click ADD.
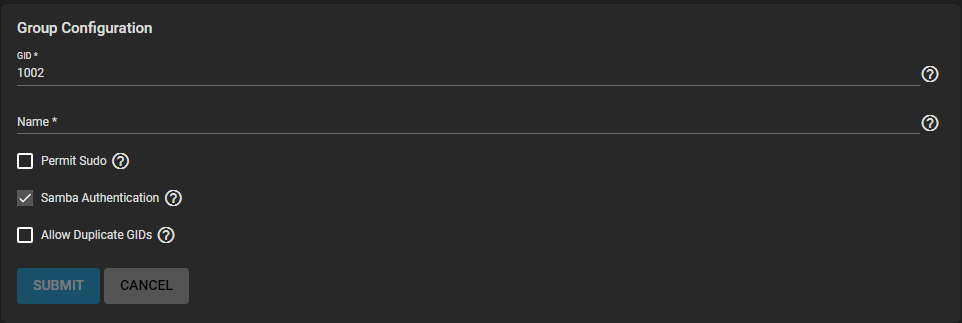
Each group gets a Group ID (GID). Enter a number above 1000 for a group with user accounts. You cannot change the GID later. Groups used by a system service must have an ID that matches the default port number used by the service.
Next, enter a descriptive group Name. Group names cannot begin with a hyphen (-) or contain a space, tab, or these characters: , : + & # % ^ ( ) ! @ ~ * ? < > =.
By default, the Permit Sudo option is unset. Setting it allows group members to act as the root account by using sudo. Leave Permit Sudo unset for better security.
Samba Authentication is set by default. It allows group members to use SMB permissions and authentication.
Finally, Allow Duplicate GIDs lets you duplicate group IDs but can complicate system configurations. We recommend leaving it unset.
Register user accounts to a group to simplify permissions and access to many user accounts. To manage group membership, go to Accounts > Groups, click the navigate_next for a group, then click group MEMBERS:
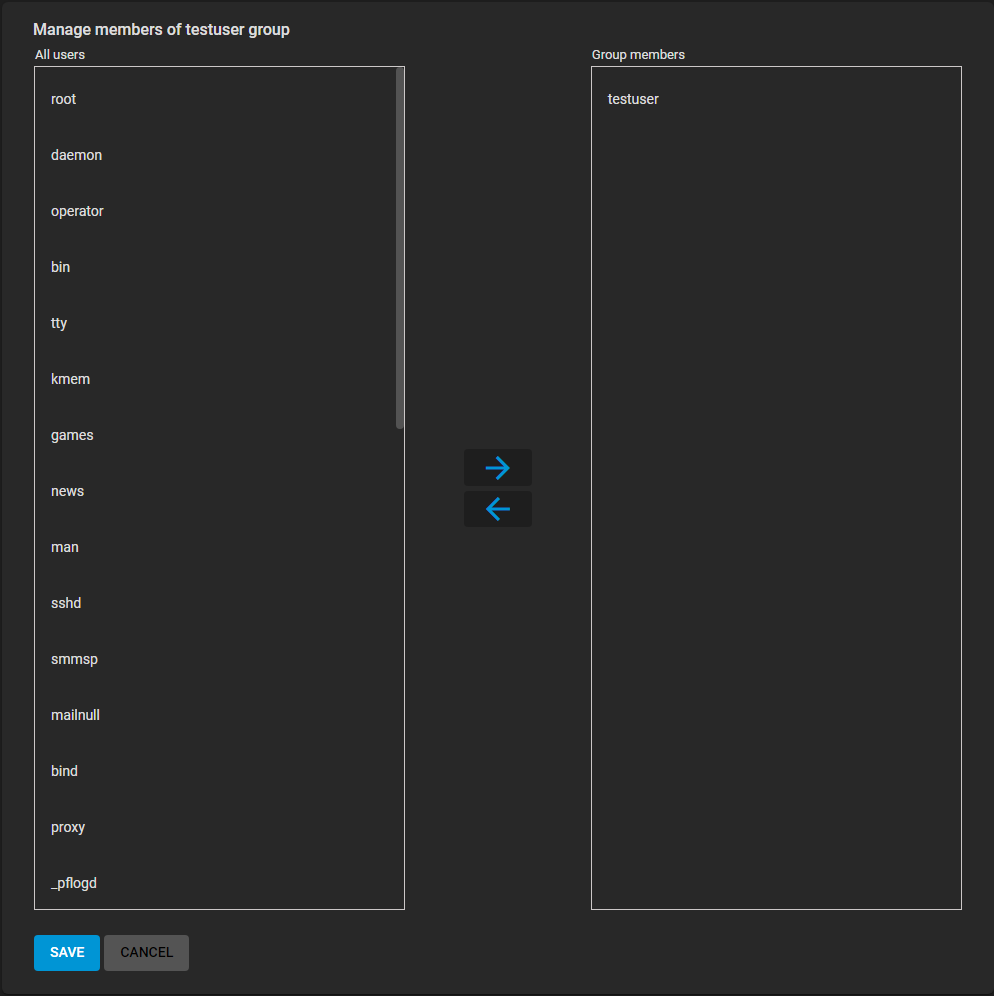
To add user accounts to the group, select them in All users and click . Select multiple users by holding CTRL while clicking each entry.

