TrueNAS CORE Nightly Development Documentation
This content follows experimental early release software. Use the Product and Version selectors above to view content specific to a stable software release.
Configuring SSH
2 minute read.
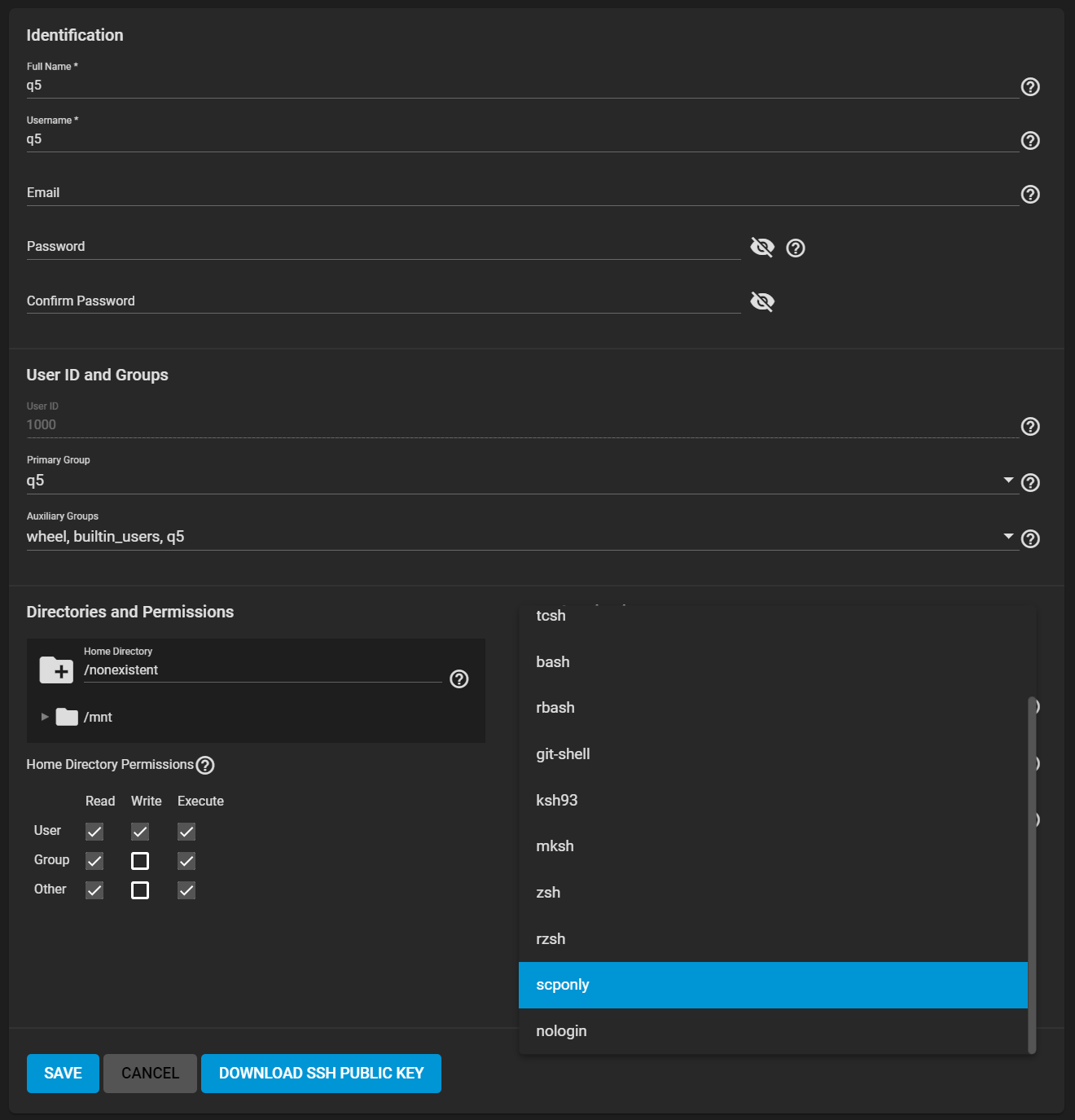
Last Modified 2024-05-08 16:06 EDTThe SSH service allows connections to TrueNAS with the Secure Shell Transport Layer Protocol. To use TrueNAS as an SSH server, the users in the network must use SSH client software to transfer files with SSH.
Allowing external connections to TrueNAS is a security vulnerability! Only enable SSH when there is a need for external connections. See Security Recommendations for more security considerations when using SSH.
To configure SSH, disable the service and click the edit.
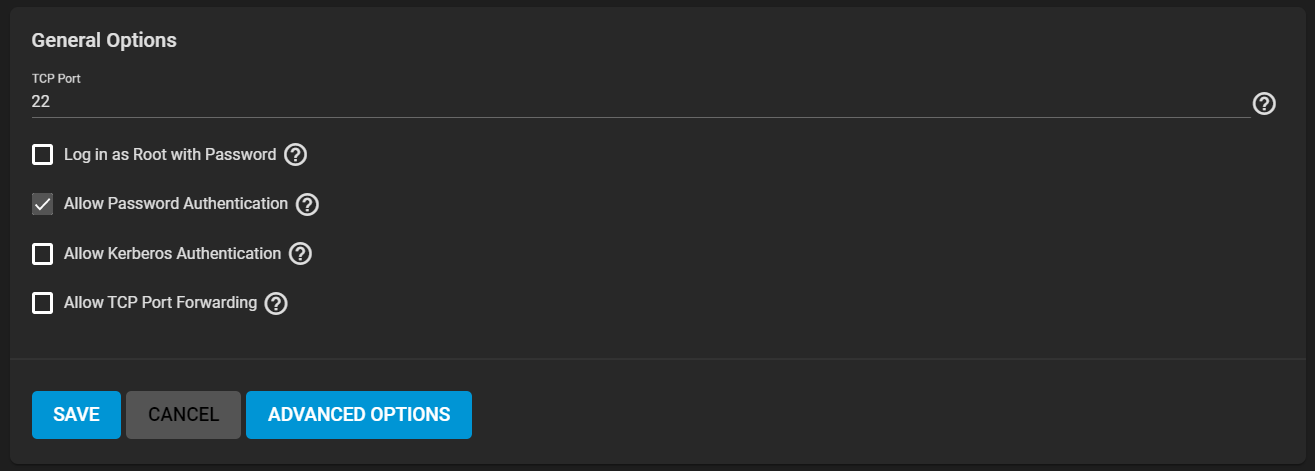
Configure the options as needed to match your network environment.
See SSH Screen
Root access to the system from a remote client is never recommended. If an unavoidable critical situation requires allowing root access, it is recommended to configure two-factor authentication first. Also, disable root logins as soon as possible.
Re-enable the SSH service on the Services page when all configuration changes are complete. To create and store specific SSH connections and keypairs, go to the System menu section.